MikroTik Tutorial: How to Export ARP, DHCP, and Routing Tables Using the file= Parameter
Picture this scenario: You receive a call at 2 AM about a network issue. You need to compare the current ARP table against yesterday’s data. Or perhaps a compliance auditor requests documentation of your DHCP lease assignments. How do you capture this data efficiently?
MikroTik RouterOS does not support traditional Linux-style output redirection. You cannot pipe command output to a file using > or >>. Instead, RouterOS provides the file= parameter.
What This Tutorial Covers
- How to use the
file=parameter across multiple command contexts - Exporting ARP tables, DHCP leases, routing tables, and firewall rules
- Automating exports with scripts and the scheduler
- Building practical workflows for documentation and troubleshooting
- Differences between RouterOS v6.x and v7.x
Who This Tutorial Is For
- Network engineers managing MikroTik infrastructure
- Systems administrators responsible for network documentation
- Security professionals conducting audits
- Anyone who needs to capture runtime data from RouterOS devices
Understanding the MikroTik file= Parameter
What Is the file= Parameter?
The file= parameter is an argument available on print, export, and certain other RouterOS commands. It redirects command output to a file stored on the router’s filesystem.
Key Characteristics
- Storage location: Files are saved to the router’s internal storage, accessible via
/file print - Default formats:
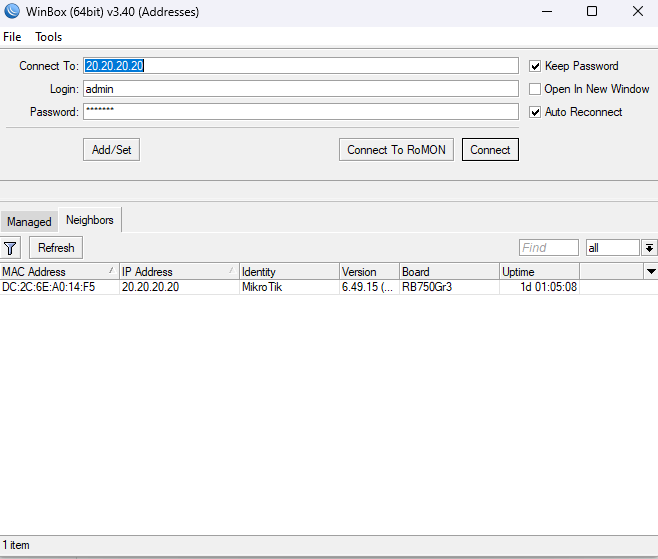
.txtforprint file=,.rscforexport file= - File retrieval: Download via WinBox drag-and-drop, FTP, SFTP, or SCP
Basic Syntax
/path/to/menu print file=filenameExample Commands
# Save ARP table to file
/ip arp print file=arp-table
# View saved files
/file print
# Download file details
/file print detailFilename Best Practices
- Use descriptive names:
arp-table-2024-01-15 - Avoid special characters except hyphens and underscores
- Keep names under 64 characters
- Include dates for historical tracking
Storage Considerations
- Check available space:
/system resource print - hAP series devices have limited flash storage (16-128 MB)
- CCR series devices have larger storage capacity
- Regularly delete old export files to prevent storage exhaustion
Saving the ARP Table to a File on MikroTik
Why Export the ARP Table?
- Troubleshoot IP conflicts and duplicate MAC addresses
- Conduct security audits and detect ARP spoofing
- Document connected devices for inventory purposes
- Create baseline comparisons over time
- Support forensic analysis during incidents
Basic ARP Table Export
# Standard export
/ip arp print file=arp-table
# Result: Creates arp-table.txt in /fileExport with Detail Modifier
The detail modifier includes all available fields in a readable format.
/ip arp print detail file=arp-table-detailExport with Terse Modifier
The terse modifier creates machine-parseable output, useful for scripting.
/ip arp print terse file=arp-table-terseFiltered Export Examples
# Export ARP entries for a specific interface
/ip arp print where interface=ether1 file=arp-ether1
# Export only dynamic entries
/ip arp print where dynamic=yes file=arp-dynamic
# Export entries for a specific subnet
/ip arp print where address~"192.168.1" file=arp-subnet1Sample Output
Flags: X - disabled, I - invalid, H - DHCP, D - dynamic, P - published, C - complete
# ADDRESS MAC-ADDRESS INTERFACE
0 DC 192.168.1.1 AA:BB:CC:DD:EE:01 bridge1
1 DC 192.168.1.10 AA:BB:CC:DD:EE:02 bridge1
2 DC 192.168.1.15 AA:BB:CC:DD:EE:03 bridge1Saving DHCP Lease Tables on MikroTik
Why Export DHCP Leases?
- Track active versus expired leases
- Document IP assignments for compliance audits
- Reference data during router migrations
- Plan DHCP pool capacity
- Identify rogue devices by hostname or MAC
Basic DHCP Lease Export
/ip dhcp-server lease print file=dhcp-leasesDetailed DHCP Lease Export
Use detail to capture hostname, MAC address, expiry time, and other fields.
/ip dhcp-server lease print detail file=dhcp-leases-detailFiltered DHCP Exports
# Export only active (bound) leases
/ip dhcp-server lease print where status=bound file=active-leases
# Export leases from a specific DHCP server
/ip dhcp-server lease print where server=dhcp1 file=dhcp1-leases
# Export static lease assignments only
/ip dhcp-server lease print where dynamic=no file=static-leasesRelated DHCP Data Exports
# Export DHCP network configurations
/ip dhcp-server network print file=dhcp-networks
# Export IP pool definitions
/ip pool print file=ip-pools
# Export DHCP server settings
/ip dhcp-server print file=dhcp-serversSample DHCP Lease Output
Flags: X - disabled, R - radius, D - dynamic, B - blocked
# ADDRESS MAC-ADDRESS HOST-NAME SERVER STATUS LAST-SEEN
0 D 192.168.1.100 AA:BB:CC:11:22:33 workstation1 dhcp1 bound 1m15s
1 D 192.168.1.101 AA:BB:CC:11:22:34 laptop-john dhcp1 bound 5m30s
2 192.168.1.50 AA:BB:CC:11:22:35 printer1 dhcp1 bound 2h10mImportant Distinction
Runtime data vs. Configuration:
print file=captures current lease state (runtime data)export file=captures DHCP server configuration (re-importable)- Dynamic leases are runtime data and cannot be imported to another router
Other MikroTik Tables You Can Save with file=
Routing Table Export
# IPv4 routing table
/ip route print file=routing-table
# IPv6 routing table
/ipv6 route print file=ipv6-routes
# Filter by route type
/ip route print where static=yes file=static-routes
/ip route print where ospf=yes file=ospf-routes
/ip route print where bgp=yes file=bgp-routes
# Include route details
/ip route print detail file=routes-detailUse case: Compare routing tables before and after maintenance windows.
Firewall Filter and NAT Rules
# Firewall filter rules
/ip firewall filter print file=firewall-rules
# NAT rules
/ip firewall nat print file=nat-rules
# Mangle rules
/ip firewall mangle print file=mangle-rules
# Include packet and byte counters
/ip firewall filter print stats file=firewall-stats
/ip firewall nat print stats file=nat-stats
# Address lists
/ip firewall address-list print file=address-listsInterface and Traffic Data
# All interfaces
/interface print file=interfaces
# Interface statistics (TX/RX counters)
/interface print stats file=interface-stats
# Ethernet interface details
/interface ethernet print file=ethernet-details
# Interface traffic snapshot
/interface monitor-traffic ether1 once file=traffic-snapshotNeighbor Discovery Tables
# MNDP/CDP/LLDP neighbors
/ip neighbor print file=neighbors
# Detailed neighbor information
/ip neighbor print detail file=neighbors-detailUse case: Map network topology and document connected devices.
DNS Cache
/ip dns cache print file=dns-cache
/ip dns cache print detail file=dns-cache-detailUse case: Investigate suspicious DNS queries during security incidents.
Bridge MAC Address Table
# MAC address table (bridge hosts)
/interface bridge host print file=mac-table
# Filter by bridge interface
/interface bridge host print where bridge=bridge1 file=bridge1-macsUse case: Layer 2 troubleshooting and loop detection.
Wireless Registration Table
# Connected wireless clients
/interface wireless registration-table print file=wireless-clients
# Detailed wireless client information
/interface wireless registration-table print detail file=wireless-detailSystem Log Export
/log print file=system-log
# Filter by topic
/log print where topics~"firewall" file=firewall-log
/log print where topics~"dhcp" file=dhcp-logUse case: Capture logs before buffer rotation overwrites them.
BGP, OSPF, and MPLS Tables
RouterOS v6 Syntax
# BGP data
/routing bgp peer print file=bgp-peers
/routing bgp advertisements print file=bgp-advertisements
# OSPF data
/routing ospf neighbor print file=ospf-neighbors
/routing ospf lsa print file=ospf-lsa-database
/routing ospf interface print file=ospf-interfaces
# MPLS data
/mpls forwarding-table print file=mpls-fibRouterOS v7 Syntax
# Note: v7 uses different command paths
/routing/route/print file=routes-v7
/routing/bgp/session/print file=bgp-sessions-v7
/routing/ospf/neighbor/print file=ospf-neighbors-v7print file= vs. export file= — Key Differences
Understanding the difference between these two commands is critical for proper data management.
When to Use print file=
- Capture runtime or dynamic data (ARP entries, DHCP leases, active routes)
- Create human-readable snapshots
- Export data that is NOT part of saved configuration
- Generate documentation for audits
- Output format:
.txt - Cannot be re-imported
When to Use export file=
- Back up configuration in script format
- Create re-importable configuration files
- Migrate configurations between routers
- Version control router configurations
- Output format:
.rsc - Can be re-imported with
/import
Comparison Table
| Feature | print file= |
export file= |
|---|---|---|
| Output format | .txt | .rsc |
| Re-importable | No | Yes |
| Shows runtime data | Yes | No |
| Shows configuration | Partially | Yes |
| Includes dynamic entries | Yes | No |
| Use case | Documentation, troubleshooting | Backup, migration |
Export Command Options
# Compact export (excludes defaults)
/export file=config-compact
# Verbose export (includes all settings)
/export verbose file=config-verbose
# Scoped export (specific section only)
/ip firewall export file=firewall-config
/ip address export file=ip-addresses-config
/interface export file=interfaces-configAutomating Table Exports with MikroTik Scheduler and Scripts
Why Automate Exports?
- Create periodic snapshots for compliance requirements
- Enable change detection and configuration drift monitoring
- Generate pre-maintenance baseline data automatically
- Reduce manual documentation effort
- Support incident response with historical data
Basic Script: Export Multiple Tables
# Script name: export-tables
# Description: Exports ARP, DHCP, and routing tables
/ip arp print file=arp-table
/ip dhcp-server lease print file=dhcp-leases
/ip route print file=routing-table
/ip firewall filter print stats file=firewall-stats
/log print file=system-logAdvanced Script: Timestamped Filenames
# Script name: export-tables-dated
# Description: Exports tables with date-stamped filenames
:local date [/system clock get date]
:local time [/system clock get time]
# Replace characters that cause issues in filenames
:local dateStr [:pick $date 0 11]
# Export with timestamp
/ip arp print file=("arp-" . $dateStr)
/ip dhcp-server lease print file=("dhcp-" . $dateStr)
/ip route print file=("routes-" . $dateStr)
:log info "Table export completed"RouterOS v7 Date Handling
# v7 has different date format
:local date [/system clock get date]
# Format: 2024-01-15
/ip arp print file=("arp-" . $date)Scheduling Automated Exports
# Add daily export at midnight
/system scheduler add \
name=daily-table-export \
interval=24h \
start-time=00:00:00 \
on-event="/system script run export-tables-dated" \
policy=read,write,test
# Add hourly ARP export
/system scheduler add \
name=hourly-arp-export \
interval=1h \
on-event="/ip arp print file=arp-hourly" \
policy=read,write
# Add weekly full export
/system scheduler add \
name=weekly-full-export \
interval=7d \
start-time=02:00:00 \
on-event="/system script run export-all-tables" \
policy=read,write,testRequired Script Policies
Scheduled scripts require specific policies to execute:
- read: Required to read table data
- write: Required to create files
- test: Required for some script functions
- ftp: Required if uploading files
- policy: Required to modify user policies
Automated File Retrieval from MikroTik
Method 1: SCP with SSH Keys
# From Linux server, pull files via SCP
scp admin@192.168.1.1:/arp-table.txt /backups/mikrotik/
# Automate with cron
0 1 * * * scp admin@192.168.1.1:/*.txt /backups/mikrotik/Method 2: Push Files Using Fetch Tool
# Upload to FTP server
/tool fetch \
url="ftp://backup-server/mikrotik/" \
src-path=arp-table.txt \
user=ftpuser \
password=ftppass \
upload=yes
# Upload to SFTP server (RouterOS v7)
/tool fetch \
url="sftp://backup-server/mikrotik/arp-table.txt" \
src-path=arp-table.txt \
user=sftpuser \
upload=yesMethod 3: Integration with Automation Tools
- Oxidized: Automated network configuration backup
- RANCID: Network configuration management
- Ansible: Use
community.routeroscollection - Git: Version control exported configurations
File Cleanup Script
# Script name: cleanup-old-exports
# Description: Removes export files older than 30 days
:local cutoffDate [/system clock get date]
# Implementation varies based on date comparison needs
# Simple approach: remove all files matching a pattern
/file remove [find where name~"arp-" and name~".txt"]
# Or remove specific old files manually identified
:foreach file in=[/file find where name~"arp-2024-01"] do={
/file remove $file
}
:log info "Old export files cleaned up"Complete Automation Script Example
# Script name: full-export-and-upload
# Description: Export tables, upload to server, cleanup
# Set variables
:local date [/system clock get date]
:local hostname [/system identity get name]
:local ftpServer "192.168.100.10"
:local ftpUser "backup"
:local ftpPass "secretpassword"
# Export tables
/ip arp print file=("arp-" . $hostname . "-" . $date)
/ip dhcp-server lease print file=("dhcp-" . $hostname . "-" . $date)
/ip route print file=("routes-" . $hostname . "-" . $date)
/ip firewall filter print stats file=("fw-" . $hostname . "-" . $date)
# Wait for file operations to complete
:delay 5s
# Upload files to FTP server
:foreach file in=[/file find where name~$date] do={
:local fileName [/file get $file name]
/tool fetch url=("ftp://" . $ftpServer . "/backups/" . $fileName) \
src-path=$fileName \
user=$ftpUser \
password=$ftpPass \
upload=yes
}
# Log completion
:log info ("Export and upload completed: " . $date)Practical Use Cases and Real-World Scenarios
Scenario 1: Pre- and Post-Maintenance Comparison
Situation: You plan to add new static routes during a maintenance window.
Procedure:
- Export routing table before changes:
/ip route print file=routes-pre-maintenance - Perform maintenance tasks
- Export routing table after changes:
/ip route print file=routes-post-maintenance - Download both files and compare using diff:
diff routes-pre-maintenance.txt routes-post-maintenance.txt - Identify unexpected changes and investigate
Scenario 2: Security Incident Response
Situation: You suspect a network breach and need to collect evidence.
Immediate Actions:
# Capture ARP table for MAC-to-IP mapping
/ip arp print file=incident-arp
# Capture DHCP leases for device identification
/ip dhcp-server lease print detail file=incident-dhcp
# Capture DNS cache for query history
/ip dns cache print file=incident-dns
# Capture firewall counters for traffic analysis
/ip firewall filter print stats file=incident-firewall
# Capture NAT table
/ip firewall nat print stats file=incident-nat
# Capture connection tracking table
/ip firewall connection print file=incident-connections
# Capture full system log
/log print file=incident-log
# Capture neighbor discovery
/ip neighbor print file=incident-neighborsPost-Collection:
- Download all files immediately
- Store files in a secure location with write protection
- Document chain of custody
- Compare against known-good baseline data
Scenario 3: DHCP Migration Between Routers
Situation: You need to migrate DHCP services to a new MikroTik router.
Important Note: Dynamic DHCP leases cannot be imported. Only static configuration can be migrated.
Procedure:
- Export DHCP configuration (re-importable):
/ip dhcp-server export file=dhcp-server-config /ip pool export file=dhcp-pool-config - Export current leases for reference (not importable):
/ip dhcp-server lease print detail file=dhcp-leases-reference - Import configuration on new router:
/import file=dhcp-server-config.rsc /import file=dhcp-pool-config.rsc - Manually recreate critical static leases based on reference file
- Allow dynamic leases to re-establish naturally
Scenario 4: Network Documentation and Compliance Auditing
Situation: An auditor requests documentation of firewall rules and network access controls for PCI-DSS compliance.
Documentation Export Script:
# Create comprehensive network documentation
# Date for file naming
:local date [/system clock get date]
:local prefix ("audit-" . $date . "-")
# Firewall documentation
/ip firewall filter print detail file=($prefix . "firewall-filter")
/ip firewall nat print detail file=($prefix . "firewall-nat")
/ip firewall mangle print detail file=($prefix . "firewall-mangle")
/ip firewall address-list print file=($prefix . "address-lists")
# Network configuration
/ip address print file=($prefix . "ip-addresses")
/ip route print file=($prefix . "routes")
/interface print file=($prefix . "interfaces")
# Access control
/user print file=($prefix . "users")
/ip service print file=($prefix . "services")
/ip ssh print file=($prefix . "ssh-settings")
# DHCP documentation
/ip dhcp-server print file=($prefix . "dhcp-servers")
/ip dhcp-server network print file=($prefix . "dhcp-networks")
/ip pool print file=($prefix . "pools")
:log info "Audit documentation export completed"Tips, Tricks, and Common Pitfalls
Best Practices
- Use descriptive filenames: Include date, device name, and content type
- Use
tersefor parsing: Easier to process with scripts and tools - Use
detailfor review: Better for human readability - Schedule regular exports: Daily or weekly depending on change frequency
- Monitor storage space: Prevent router storage exhaustion
- Implement file rotation: Delete old files automatically
- Copy files off-router: Router storage is not a backup location
Common Mistakes to Avoid
| Mistake | Consequence | Solution |
|---|---|---|
Confusing print file= with export file= |
Attempting to import non-importable files | Use export for config backup, print for snapshots |
| Missing script policies on scheduler | Scheduled exports fail silently | Add read, write, test policies |
| Using same filename repeatedly | Files overwritten, no history | Include timestamps in filenames |
| Not cleaning up old files | Router storage fills up | Implement cleanup script |
| Storing sensitive data insecurely | Security and compliance issues | Use secure transfer methods, encrypt storage |
RouterOS v7 Differences
- New command paths: Many commands use
/routing/instead of/routing - Date format change: v7 uses
YYYY-MM-DDformat by default - New routing syntax:
# v6 syntax /ip route print file=routes # v7 syntax /routing/route/print file=routes - REST API: v7 supports REST API for data extraction in JSON format
- Container support: v7 can run containers for advanced data processing
Filename Character Limitations
- Allowed characters: letters, numbers, hyphens, underscores, periods
- Avoid: spaces, colons, slashes, special characters
- Maximum length: 64 characters recommended
- RouterOS auto-appends extension (.txt or .rsc)
Flash Storage Wear Considerations
MikroTik devices use flash storage with limited write cycles:
- Avoid excessive write operations on small devices
- Export to RAM disk when available:
/file print where name~"ramdisk" - Use external USB storage on supported devices
- Transfer files off-router promptly
Alternative Methods for Extracting Data from MikroTik
The file= parameter is one of several methods to extract data from RouterOS. Consider these alternatives based on your requirements.
MikroTik API (RouterOS API)
- Protocol: Custom binary protocol on port 8728 (or 8729 for SSL)
- Languages: Python (routeros_api, librouteros), PHP, Ruby, Go
- Use case: Programmatic access, automation, monitoring integration
Python Example:
import routeros_api
connection = routeros_api.RouterOsApiPool('192.168.1.1', username='admin', password='password')
api = connection.get_api()
# Get ARP table
arp_table = api.get_resource('/ip/arp').get()
for entry in arp_table:
print(entry)REST API (RouterOS v7 Only)
- Protocol: HTTP/HTTPS on configurable port
- Format: JSON responses
- Use case: Integration with modern automation tools, web applications
REST API Example:
# Enable REST API
/ip/service/set www-ssl disabled=no
# Query via curl
curl -k -u admin:password https://192.168.1.1/rest/ip/arpSNMP
- Protocol: SNMP v1/v2c/v3 on UDP port 161
- Use case: Monitoring systems, network management platforms
- Data available: Interfaces, routes, ARP, system health
Enable SNMP:
/snmp set enabled=yes
/snmp community add name=public addresses=192.168.1.0/24Syslog Forwarding
- Use case: Centralized log collection and analysis
- Configuration:
/system logging action add name=remote target=remote remote=192.168.1.100 /system logging add topics=info action=remote
The Dude Network Monitor
- Product: Free MikroTik network monitoring application
- Capabilities: Automatic device discovery, monitoring, data collection
- Use case: Visual network mapping, historical data
Comparison: When to Use Each Method
| Method | Best For | Complexity |
|---|---|---|
file= |
Quick snapshots, scheduled exports, simple automation | Low |
| RouterOS API | Custom applications, real-time data access | Medium |
| REST API | Modern integrations, web services | Medium |
| SNMP | Monitoring platforms, legacy systems | Low-Medium |
| Syslog | Log aggregation, security monitoring | Low |
Conclusion: Build a Habit of Exporting MikroTik Data
Key Takeaways
- The
file=parameter enables export of runtime data that is not saved in configuration - Use
print file=for snapshots and documentation - Use
export file=for re-importable configuration backups - Automate exports with scripts and the scheduler
- Implement file rotation to manage storage
- Transfer files off-router for long-term retention
Quick Reference Commands
# ARP table
/ip arp print file=arp-table
# DHCP leases
/ip dhcp-server lease print file=dhcp-leases
# Routing table
/ip route print file=routes
# Firewall rules with counters
/ip firewall filter print stats file=firewall
# System log
/log print file=system-log
# View saved files
/file print
# Delete old files
/file remove arp-table.txtNext Steps
- Create a script that exports your critical tables
- Schedule the script to run daily
- Set up automated file retrieval to a backup server
- Implement file cleanup to manage storage
- Document your export workflow for your team
Start with a simple scheduled ARP table export today. Build from there as you identify additional data worth capturing.
Check our list of MikroTik guides